Notices by Joshua Judson Rosen (rozzin) tagged crypto
-
Joshua Judson Rosen (rozzin)'s status on Monday, 01-Jul-2019 15:50:40 EDT  Joshua Judson Rosen
Joshua Judson Rosen
ALSO, I'm reminded that there was this other #HKP #keyserver released a few years ago, compatible w/ #SKS but written in #Golang, which might relieve some of "zomg unmaintainable!" problems with the SKS servers: https://hockeypuck.github.io/ !crypto #PGP #GnuPG -
Joshua Judson Rosen (rozzin)'s status on Monday, 01-Jul-2019 15:42:36 EDT  Joshua Judson Rosen
Joshua Judson Rosen
Also it seems kind of inappropriate to be using "poisoning" as its being used here: https://gist.github.com/rjhansen/67ab921ffb4084c865b3618d6955275f !crypto -
Joshua Judson Rosen (rozzin)'s status on Monday, 01-Jul-2019 15:40:24 EDT  Joshua Judson Rosen
Joshua Judson Rosen
@boneidol The signature-flooding attack on the SKS #keyservers (and DoS of their users) is bad but doesn't actually sound like any kind of #apocalypse, and has basically nothing to do with the #WoT; signature-chains maybe, but that's something else entirely. !crypto -
Joshua Judson Rosen (rozzin)'s status on Friday, 28-Sep-2018 16:37:05 EDT  Joshua Judson Rosen
Joshua Judson Rosen
With the sudden realization that #Enigmail has been able to decrypt #email permanently upon reception for the last 3 years, I'm excited about using #PGP #crypto w/ #Enigmail again! But, oh, just in time for me #Mozilla broke Enigmail in #Debian: https://bugs.debian.org/cgi-bin/bugreport.cgi?bug=909000 #ugh -
Joshua Judson Rosen (rozzin)'s status on Friday, 28-Sep-2018 16:22:38 EDT  Joshua Judson Rosen
Joshua Judson Rosen
Holy crap! "Since version 1.8, Enigmail can decrypt mails permanently." https://enigmail.net/index.php/en/faq-en?view=topic&id=15 #enigmail #pgp #crypto -
Joshua Judson Rosen (rozzin)'s status on Wednesday, 12-Sep-2018 10:21:27 EDT  Joshua Judson Rosen
Joshua Judson Rosen
I actually do really want to secure my data in transit; but it's frustrating to the point of deterrence that the tools for secure transit seem to frequently create more problems for data at rest. #Enigmail maintained similar barriers to PGP use for years, for example: http://status.hackerposse.com/conversation/44450#notice-52884 #crypto -
Joshua Judson Rosen (rozzin)'s status on Tuesday, 22-Mar-2016 23:17:35 EDT  Joshua Judson Rosen
Joshua Judson Rosen
Met a bunch of awesome people at #lp2016. And few... #interesting ones. Like the one who refused to sign my #PGP key because she thought I was a government spook... because I claimed to be from #NH but "didn't know that *every* FreeStater is (obviously) #crypto savvy enough to sign PGP keys... since most of them use #bitcoin as their only currency... so they can remain anonymous". #wtf #notevenwrong -
Joshua Judson Rosen (rozzin)'s status on Saturday, 14-Feb-2015 18:47:12 EST  Joshua Judson Rosen
Joshua Judson Rosen
"The #Debian #PGP #disaster that almost was": http://rdist.root.org/2009/05/17/the-debian-pgp-disaster-that-almost-was/ !crypto -
Joshua Judson Rosen (rozzin)'s status on Monday, 02-Feb-2015 23:04:12 EST  Joshua Judson Rosen
Joshua Judson Rosen
@boneidol, we need to get past the idea that !crypto's too complicated & too slow for everyday use. It works better than the alternatives. -
Former Bob Jonkman -- Please use the new server at https://gs.jonkman.ca (bobjonkmanformer)'s status on Monday, 10-Nov-2014 00:53:21 EST  Former Bob Jonkman -- Please use the new server at https://gs.jonkman.ca
Former Bob Jonkman -- Please use the new server at https://gs.jonkman.ca
My presentation notes on !Tor for the @GTALUG "Short talks on !Crypto" on Tuesday are now online: http://sobac.com/gtalug -
Joshua Judson Rosen (rozzin)'s status on Monday, 03-Nov-2014 00:09:40 EST  Joshua Judson Rosen
Joshua Judson Rosen
@lnxw48, if you can verify via #crypto the #goodguy #identity of the file-provider and/or file, address doesn't really matter. That's what makes using mirrors of signed packages viable. -
lnxw48 (Linux Walt) (lnxw48)'s status on Thursday, 25-Sep-2014 04:57:39 EDT  lnxw48 (Linux Walt)
lnxw48 (Linux Walt)
@vegos Patch does not completely fix the issue. New CVE number issued. http://url.federati.net/rS61B !security !crypto
-
Joshua Judson Rosen (rozzin)'s status on Sunday, 02-Mar-2014 19:15:42 EST  Joshua Judson Rosen
Joshua Judson Rosen
@boneidol, something like that: https://en.wikipedia.org/wiki/Birthday_attack#Mathematics !crypto -
Joshua Judson Rosen (rozzin)'s status on Sunday, 02-Mar-2014 16:47:52 EST  Joshua Judson Rosen
Joshua Judson Rosen
#git practically advocates abbreviating SHA-1 !crypto hashes to 7 hexits; #redmine habitually abbreviates them to 8; somehow this never collides with the notion that "the unlikelihood of hash-collisions is astronomical because it's SHA-1". -
Joshua Judson Rosen (rozzin)'s status on Sunday, 02-Mar-2014 16:40:39 EST  Joshua Judson Rosen
Joshua Judson Rosen
For every person who understands all of the implications of abbreviating a !crypto #hash, I wouldn't be surprised if there are a million who can't imagine there's any problem. -
Joshua Judson Rosen (rozzin)'s status on Sunday, 02-Mar-2014 15:18:51 EST  Joshua Judson Rosen
Joshua Judson Rosen
The #problem w/ #checksum as #ID: users need basic understanding of the nature of a !crypto #hash. http://status.hackerposse.com/url/5412 -
Joshua Judson Rosen (rozzin)'s status on Friday, 21-Feb-2014 21:31:41 EST  Joshua Judson Rosen
Joshua Judson Rosen
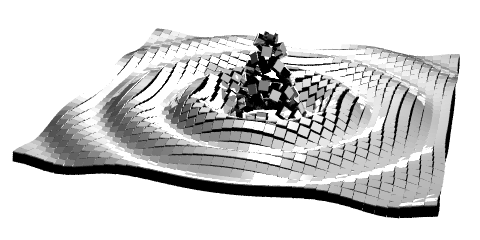
I like @robmyers' post about !crypto #sigils: http://robmyers.org/2014/02/07/crypto-sigils/ !visualids -
Joshua Judson Rosen (rozzin)'s status on Wednesday, 01-Jan-2014 15:50:26 EST  Joshua Judson Rosen
Joshua Judson Rosen
http://www.xylocopa.com/product/mad-science-alphabet-blocks doesn't tell you, but the package teaches: the blocks work as #babysfirst #rot13 !crypto #kit ☺ -
Joshua Judson Rosen (rozzin)'s status on Sunday, 10-Nov-2013 00:05:30 EST  Joshua Judson Rosen
Joshua Judson Rosen
#q "I'm sorry, but looking at my large list of tools available to me, the one labelled #Democracy seems far more likely to get me what I want than one labelled "Amateur #Crypto"." http://slashdot.org/comments.pl?sid=4383783&cid=45256675 -
Joshua Judson Rosen (rozzin)'s status on Saturday, 09-Nov-2013 20:40:39 EST  Joshua Judson Rosen
Joshua Judson Rosen
"HTTPS is great: here's why everyone needs to use it (so we can too)": why nobody wants to be first; #oversplification hurting !crypto !security? http://status.hackerposse.com/url/4193